Jen Easterly, Director of the Cybersecurity and Infrastructure Security Agency (CISA), stated at a November 1 Center for Strategic and International Studies (CSIS) event that CISA does not "censor information." Information revealed in the Twitter Files and Biden v. Missouri might lead one to disagree with this position. Nevertheless, here is what she said:
"I want to be really clear about what CISA's role is in this. You know, we are not an intel agency. We're not a law enforcement agency. We don't work with the platforms on what they do around content. That is entirely their decision. It is their terms of service.
And I want to be very clear about this, we do not censor information. Securing elections is a nonpartisan activity, and quite frankly, as somebody who's worked in Democratic and Republican administrations, you know, as somebody's who served the American people my whole life—in peacetime, in combat, sworn to defend and protect the Constitution of the United States—including, and in particular, the First Amendment—I want to be very clear, we do not censor anything. What social media platforms do, what the news does is entirely their decision."
Easterly then went on to admit the things her organization does do. She states CISA has a "cyber and physical and information cognitive piece." Then she speaks to the cognitive piece. "What do we do?" she asks. "It is three things." It is her euphemistic version of the truth behind what is, yes, censorship. I will help translate it here.
Easterly: "We make sure that people understand the tactics around disinformation and that Americans understand, you know, how to build resilience against it, how to recognize it, how to investigate it, asking about the source, questioning it, not amplifying it—all of that's incredibly important."
Translation: We, the proper purveyors of the correct information, want to make sure you peons who cannot think for yourselves know how to ignore, spot, interpret, and definitely not spread stuff we don't condone.
Easterly: "We have an election security rumor versus reality website, and what does that do? It's election literacy. You talk a lot about civics education—it's election literacy. And so, you know, elections are super complicated. It's information that's out there—like, what is accurate?"
Translation: We control what defines rumor and what defines reality; you're welcome. This is how you know what is really going on with elections. The unwashed masses cannot possibly understand elections. We can't have public discourse defining the truth. Like, we have to make sure what they see is accurate.
Easterly: "And then, most importantly, we amplify the voices. We amplify the voices— of those trusted voices—state and local election officials, who are the people that people should go to. If you have any questions at all about voting, how voting works, go to your state and local election officials."
Translation: Listen up. We must ensure the right people are prioritized, which means the voices of the peons are deboosted, hidden, or even removed. Because we cannot have a world where the people we think should be seen and heard get lost in the shuffle. It is the only way you can know how to vote and who to vote for. So we have ways to make sure the right voices will be heard. But, yeah, no censoring whatsoever. Trust me.
Easterly's CISA: Cognitive Infrastructure is Key
Easterly is an important figure because, as Editor-in-Chief Tracy Beanz points out, she has attended every weekly meeting having to do with Election Security and Resilience (ESR), coordination between CISA and Facebook about election mis- and disinformation, CISA's Cybersecurity Advisory Committee (CSAC), the subcommittee for mis-, dis-, and malinformation (MDM), and the Election Infrastructure Subsector Government CoordinatingCouncil (EIS-GCC) and Election Infrastructure Subsector Coordinating Council (EI-SCC) Joint MDM Working Group. She was nominated for director of CISA by Biden in April 2021.
UncoverDC has written extensively about how CISA has designated Americans' thoughts as "Cognitive Infrastructure." Because they've declared what Americans decide to write on social media as infrastructure, they have decided that it also falls under their purview to manage and control. CISA and Easterly have been taking steps for years to make "cognitive infrastructure" stronger, in their image, of course. To most, that means propaganda. To CISA, it means censorship and control while ensuring only "approved" narrative is available for consumption.
In 2018 Easterly and Joshua Geltzer co-wrote a column about the "evaporation of trust" in elections. She and her colleague open the piece by thanking Special Counsel Mueller for his indictments related to the 2016 election. They also thank Facebook's Mark Zuckerberg for his testimony on, in his words, "fake news, for foreign interference in elections, and hate speech" on the platform.
However, it is in the second paragraph the pair writes about the "assault on trust in the digital age, indeed an assault on what's arguably our most critical asset: our cognitive infrastructure." They refer to this assault on trust as a "disease." Referencing a column on Just Security by Jonathon Morgan and Renee DiResta—who is one of the top disinformation collaborators for EIP—Easterly and Geltzer write about America's cognitive infrastructure and their quest to "shield it from assault" and to "protect the 'human-operating system.'"
"America's adversaries have weaponized information, or really disinformation, to infect Americans' perceptions of what's true and even of truth itself; what's more, their efforts have been deliberately embraced and amplified by politicians and media outlets here at home. No longer are facts such "stubborn things," quoting John Adams.
America's cognitive infrastructure, they say is "foundational to our country's economic and political health."
Here they also advocate for partnerships between social media companies and independent fact-checkers like Snopes.com to avoid "viral falsehoods." They conclude that "good national security policy" is only as good as "the set of facts" that define the issues we debate. "The human impulse," they write, is to "regard seeing as believing." I quote:
"It's no secret that good national security policy rests on good decision-making. But good decision-making rests on good information and basic trust that, when we debate tough issues, there's at least a set of facts in the world defining those issues. Before we can improve America's national security decision-making, we need to improve a piece of our critical infrastructure long taken for granted: our cognitive infrastructure."
Top-down control of "the facts" seems to be a guiding principle for Easterly. She and her team define who the "trusted experts" are.
As with most of these mis- and disinformation types, she uses national security to rationalize her approach. Beginning at the 16-minute mark below, Easterly speaks about the battle for the truth and the "cognitive infrastructure" in the information age. She briefly discusses building a "culture of psychological safety," the "testing out of CISA's "innovative" graphic novels, and the rumor control arm of CISA:
The Hindsight Musings of Twitter's Jack Dorsey
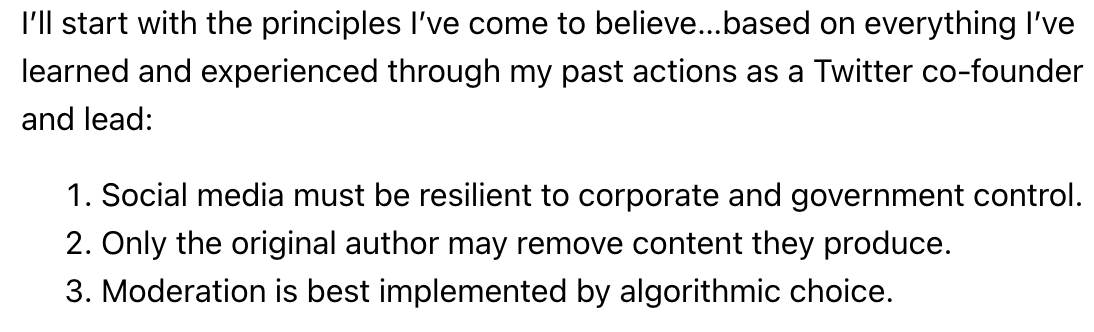
In his musings yesterday after the fallout of the ongoing Twitter Files, even former Twitter CEO Jack Dorsey seems to acknowledge how far astray these types of government and Big Tech controls have become regarding First Amendment speech. Argue as you may about how genuinely he cares or whether it is too late to voice his regrets. In truth, he lays out principles that have been pretty obvious to the censored among us. Namely, he says we should be responsible for whether our content stays or goes, not the overlords at CISA and whatever other agencies are working behind the scenes to control what we see and hear. He now sees the light and wants to give control back to the "original author" who produced the content.
 Jack Dorsey/https://www.getrevue.co/profile/jackjack/issues/a-native-internet-protocol-for-social-media-1503112?via=twitter-card&client=DesktopWeb&element=issue-card
Jack Dorsey/https://www.getrevue.co/profile/jackjack/issues/a-native-internet-protocol-for-social-media-1503112?via=twitter-card&client=DesktopWeb&element=issue-card
Instead of building tools for Twitter to "manage the public conversation," he says he now thinks he should have invested in "building tools for the people using Twitter to easily manage it for themselves." He did the "wrong thing for the internet and society." Ya think??! The sad part is that he still believes there was no "ill intent or hidden agendas, and everyone acted according to the best information we had at the time." Jack may need some reading glasses.
One can argue that censoring on the internet comes from a place of genuine concern, not ill intent, at least from a certain ideological perspective. However, there is very little doubt at this point that hidden agendas have attempted to control public dialogue for many years now, including from CISA and the now-disbanded Trust and Safety department at Twitter.


