We reported in July on documents hosted at the FBI records vault related to murdered DNC staffer Seth Rich. The release followed attorney Ty Clevenger's lawsuit after his client's FOIA request had been denied. Here we examine these documents in detail.
The 142 pages are hosted within two PDFs that we've combined here (page numbers throughout this article correspond with that upload). Pages 86-142 are the newly released documents the FBI found to be related to Seth Rich. Some of these are identical, or nearly identical, to documents previously available in the public domain, while some reveal information that we had not yet seen.
Among the documents are numerous FBI '302' forms used to summarize interviews conducted during the course of an active investigation. The 302 is a combination of an agent's recollection of what was said and incorporating any notes taken. Interviews are not typically recorded.
Similar to a police incident report, the process is prone to both unintentional inaccuracies and intentional misrepresentation. 302's have historically been used to manufacture fabricated evidence in politically sensitive cases, including General Michael Flynn's case. The witness usually has no chance to correct errors or fabrications, though there is legal precedent that a characterization therein requires corroboration to be considered fact.
A 302 report is supposed to be filed by the agent within five days after the interview being summarized, but in the release, we see many 302 filings that are dated much later:
| Page | Subject of Interview | Date Occurred | Date Entered | Difference (Days) |
| 62 | Unknown* | 09/14/16 | 09/29/16 | 15 |
| 118 | Unknown* | 09/14/16 | 09/30/16 | 16 |
| 59 | Unknown U.S. Attorney | 03/15/18 | 03/26/18 | 11 |
| 11 | Richard Gates** | 04/10/18 | 08/15/18 | 127 |
| 47 | Richard Gates** | 04/10/18 | 05/10/18 | 30 |
| 15 | Unknown | 07/02/18 | 10/21/18 | 111 |
| 12 | Jason Fishbein | 08/16/18 | 08/27/18 | 11 |
| 18 | Jason Fishbein | 09/05/18 | 10/23/18 | 48 |
| 20 | Paul Manafort | 09/27/18 | 10/31/18 | 34 |
| 71 | Paul Manafort | 10/01/18 | 11/02/18 | 32 |
| 50 | Unknown | 10/4-5/18 | 10/30/18 | 25 |
| 55 | Unknown | 10/24/18 | 11/09/18 | 16 |
| 29 | Jerome Corsi | 10/31/18 | 01/04/19 | 65 |
| 34 | Dana Rohrabacher | 10/02/19 | 03/05/20 | 155 |
* This 302 of an interview with a Seth Rich colleague whose unknown identity is almost entirely redacted. It appears twice here because it was entered by agents twice on different dates. Though they summarize the same interview, there are subtle differences between the two 302's.
** This 302 appears twice because the summary of the interview was entered 5/10 in the case for which the investigation was being conducted, and then on 8/15, it was imported into a separate case due to its relevance in that secondary matter. It isn't obvious what cases the filings relate to, but the later filing shows classification markings related to national security (NSICG).
In addition to the above, on page 24, an unknown person is said to have "voluntarily produced [redacted]" on 10/24/17, with the production both filed and uploaded digitally, but the 302 reports documenting that weren’t entered until 06/29/18.
Filing a 302 much later than the interview increases the chances that recollections will be inaccurate, or it could also be an indicator of foul play. The 302 from Peter Strzok's interview with General Flynn was dated seven months after the interview.
Some of the interviews in this release are related to the Seth Rich murder investigation, while some are related to the investigation into the breach of the Democratic National Committee (DNC) servers. Mueller's Crossfire Hurricane investigation of potential Russian interference into the 2016 U.S. Presidential election is also intertwined. Seth Rich's employment with the DNC, Wikileaks publishing of the DNC data, Crowdstrike's forensic analysis, FusionGPS providing information to DNC counsel Perkins Coie on potential Russian interference, and the attempt to impeach Trump are all related.
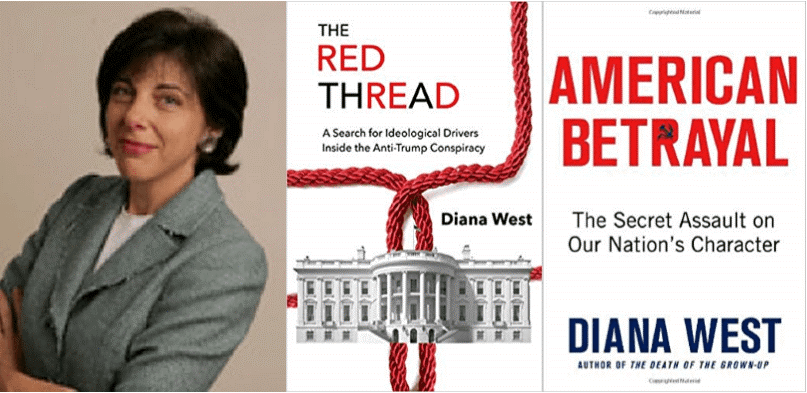 Diana West is the author of The Red Thread: A Search for Ideological Drivers Inside the Anti-Trump Conspiracy. She has compiled a Seth Rich timeline that shows us FBI Director James Comey and head of NSA Michael Rogers testified to the House Intelligence Committee on alleged Russian interference on March 20, 2017:
Diana West is the author of The Red Thread: A Search for Ideological Drivers Inside the Anti-Trump Conspiracy. She has compiled a Seth Rich timeline that shows us FBI Director James Comey and head of NSA Michael Rogers testified to the House Intelligence Committee on alleged Russian interference on March 20, 2017:
HURD: Have you been able to -- when did the DNC provide access for -- to the FBI for your technical folks to review what happened?
COMEY: Well, we never got direct access to the machines themselves. The DNC, in the spring of 2016, hired a firm that ultimately shared with us their forensics from their review of the system.
HURD: Director Rogers, did the NSA ever get access to the DNC hardware?
ROGERS: The NSA didn't ask for access. That's not in our job...
HURD: ... So director FBI notified the DNC early, before any information was put on Wikileaks and when -- you have still been -- never been given access to any of the technical or the physical machines that were -- that were hacked by the Russians.
COMEY: That's correct, although we got the forensics from the pros that they hired, which -- again, best practice is always to get access to the machines themselves, but this -- my folks tell me was an appropriate substitute.
The very next day, as shown on pages 87-90 of the new documents, FBI San Francisco contacted law firm Perkins Coie to follow up on an October 2016 request for "DNC / DCCC data." Perkins Coie is counsel for the Democratic National Committee and the Democratic Congressional Campaign Committee, and in the FBI summary of this email chain, Perkins Coie is described as "counsel for the victim." The summary report says that the Perkins Coie attorney contacted and spoke with the FBI agent on March 31, promising a detailed written response to follow. Pages 95-99, dated April 23, 2017, are redacted but contain that written response that had been promised.
Then on April 28, the FBI provides a physical mailing address of the FBI field office in San Francisco. Pages 109 and 110 are a 'Collected Item Log' report dated May 19, 2017, that tells us Perkins Coie's Washington D.C. office sent a Lenovo Thinkpad laptop to that address. That laptop is documented as being accompanied by a one-page letter and having "paper taped to the top identifying it as S. Rich laptop."
These pages are marked 'SECRET,' which is the second-highest classification level and reserved for national security information. The case information includes a notation that the evidence is related to an investigation into State-Sponsored Computer Intrusion; the Democratic National Committee is victim, and unknown subjects include Guccifer2.
Page 115 is an informational filing that references an article from CrowdStrike, whom DNC had hired to find who breached their servers, and notes that "the FBI has an ongoing investigation into the online persona known as Guccifer 2.0." The document originates from the "Office of Legal Attache at the United States Embassy," meaning it came from an FBI office in an American embassy on foreign soil. It is dated January 2, 2018, and it lists as an enclosure a "DVD with FDR Supporting Information for [redacted]." FDR may stand for Federal Data Request, Forensic Data Recovery, or Flight Data Recorder.
Numerous pages in the release show high levels of classification. Page 116 is related to the San Francisco FBI's investigation marked SECRET for its involvement with suspected State-Sponsored Computer Intrusion, with classification category 1.4 (b) for "foreign government information." It is a standard form titled "Research on Guccifer2 and DCLeaks," and the only reason for filing noted is: "To upload research." It shows that several enclosures were included, but the nature of them is redacted.
Rich's laptop evidence form was originally classified under National Security Information Classification Guidance (NSICG) per one of Obama's first Executive Orders 13526, for information that "could reasonably be expected to cause identifiable or describable damage to the national security" and pertains to "intelligence activities (including covert action), intelligence sources or methods, or cryptology."
Was Seth Rich's laptop of interest in the FBI's national security investigation into who breached the DNC servers?
Mueller's Crossfire Hurricane investigation may have wanted a look. On page 137, the latest Rich release has an email sent to L Rush Atkinson and Jeannie S. Rhee of the Special Counsel's office with the subject, "Seth Rich work laptop." It states, "...Perkins Coie provided San Francisco FBI with a copy of Seth Rich's DNC laptop. The FBI submission document says the laptop was given to the FBI voluntarily, so I am assuming that there is no Search Warrant for the laptop... San Francisco provided [redacted] for us at S[pecial] C[ounsel's] O[ffice]."
In 'Why Did Perkins Coie Have a Copy of Seth Rich's Laptop,' Diana West shows that among the documents that had been previously released by Clevenger and are also included in the new batch is a 302 summary of an interview with a United States District Attorney (AUSA), whom West says is likely Deborah Sines, that contains two bits of important information. One, there are two Seth Rich laptops -- a work laptop and a personal laptop. Two, that the AUSA had requested a "forensic image" of the work laptop for the investigation into Rich's homicide.
As West says in her article, "Perkins Coie, legal counsel of the DNC and the Hillary Clinton campaign, has its fingerprints are all over the old Russia Hoax, beginning with hiring Fusion GPS to concoct the fake Steele dossier and hiring Crowdstrike to fake-investigate the DNC email leak. Now the firm of Marc Elias (Kamala Harris campaign counsel) and Michael Sussman and Robert Bauer (wife Anita Dunn) is a link in the chain of custody of the Seth Rich laptop."
https://rumble.com/vbxq19-episode-72-the-red-thread-inside-the-anti-trump-conspiracy-part-i-wdiana-we.html
West joined Frank Gaffney of the Center for Security Policy on Bill Walton's show in an episode named after West's book The Red Thread:
WEST: "... you have the DNC people basically saying, oh my gosh, we've had this terrible event, let's not call the FBI, let's call our fixer who brings in CrowdStrike. And it's important to know that CrowdStrike is a company that is founded by a protege of Robert Mueller by the name of Sean Henry, another one of these cyber experts and, at the FBI..."
GAFFNEY: "The FBI was told, 'You don't need to look at the actual servers, CrowdStrike's got that' ... and I can't believe it, Bill, as long as I've been in Washington, I can't believe the FBI said, no problem. They didn't do the forensic deep dive themselves. They took the word of these characters."
GAFFNEY: "... the number of agencies that actually bought this was far smaller than the number we were told about, which goes to your question about the intelligence community. There are 17 agencies in the federal intelligence community, and we were told by... Hillary Clinton... in the debate with Donald Trump, she says all 17 agencies of the intelligence community say it was a Russian hack. And you know who actually is the source of this? John Brennan. John Brennan hand-picked a couple of analysts - trusted analysts who would do his bidding - and they came up with the answer that it was the Russians. Not 17 agencies. Not unanimous."
WEST: "...we talked originally about how it was that this unexpected breach of the DNC was layered into the whole Russia hoax... this is for me, is the absolute screaming headline of all of this, you get the Steele Dossier, which was really supposed to be the vehicle of the Russian collusion hoax, and this CrowdStrike redacted draft, we find out through the Roger Stone case, it wasn't even a final report that the FBI accepted, it was redacted - CrowdStrike redacted it before it gave to the FBI... the Mueller report itself, the indictment of the Russian military officers that Mueller put forward during the investigation... all of these things... court cases that have since come down... indeed the FISA abuse IG report too - they all ... rest on one or both of these two fraudulent, essentially DNC Hillary Clinton paid for documents - CrowdStrike and the Steele Dossier. So our entire history right now is being rewritten based upon utter fraudulent information... When you see anyone talk about Russian interference in the election, you can peel it back and find CrowdStrike, you can peel it back and find Steele Dossier, and sure enough, with some of these various documents, there has been confirmation by the principles themselves - Clapper, Brennan for a while... Comey... they were arguing about who actually ... asked for the Steele Dossier to be used in their very pivotal assessment of January 2017."
Seth Rich has long been suspected of being responsible for the DNC breach and could even conceivably have been asked to do it under the responsibilities of his employment there. Referring to Bill Binney's work with Veteran Intelligence Professionals for Sanity (VIPS), Gaffney explains:
"What we have heard is that the information that was leaked from the DNC was actually obtained not from an outside source that hacked into the server... the download times were sufficiently short that it made much more sense that it was simply downloaded by a thumb drive from inside the DNC itself... an inside job."
Gaffney says there are other possibilities that fit that theory:
"There's another candidate for the inside job... an outfit known informally as the Awan Brothers... Pakistani nationals who at the time were working for, among others, Debbie Wasserman Schulz, providing I.T. services to about 40 members of Congress, and using, among other things, servers in Pakistan to handle some of the information they were obtaining from Congressional sources... they had the passwords for Debbie Wasserman Schulz's computers... people at the DNC when they wanted to get her emails, they had to go to Iman Awan to get the password, which means we've got another possible explanation for how this was an inside job - not a Russian job."
West's work has paralleled that of UncoverDC in painting the bigger picture of Russiagate as it relates to the 2016 election, Wikileaks, and Seth Rich. She later adds:
"...this notion that Russia installed Donald Trump... when you see who doesn't want to open it up, doesn't want to interview Binney or Assange, or look at what happened - you have to suspect that they are in and of the swamp and that they are part of the movement to prevent Trump from being successful and re-elected and supported."
Gaffney describes CIA director John Brennan's potential role:
"Seymour Hersh said that the Trump/Russia disinformation campaign was started by Brennan ... John Brennan was a Democratic political operative as well as somebody who worked in the Central Intelligence Agency, and the previous role, before he went to the CIA, he was Barrack Obama's... Homeland Security advisor, so he was very close to the president, and he was an obvious candidate to run an operation like this that was aimed at making Donald Trump a Russian dupe, making him a co-conspirator with the Russians and influencing our election."
FOIA Attorney Clevenger succeeded in forcing the release of these documents that may not have otherwise been public in the near term. On June 15, Clevenger went further and filed a Motion to Compel requesting the court make the FBI show unredacted versions of the documents, with June 28 FBI counsel responding on June 28. Obama appointee Judge Amos Louis Mazzant III sided with the argument from the FBI and denied Clevenger's Motion to Compel on July 6.
Per Diana West:
"For several crucial years, the FBI denied investigating Seth Rich at all; for several crucial years, the FBI denied having any documents related to any such investigation; for several crucial years, the FBI denied having possession of Seth Rich's laptop. We now know the FBI lied about every one of these things and so many more."
Though many questions remain, the new releases and open source information available to the public represent many pieces to a much larger puzzle. In the 'Red Thread' episode of his show, Walton notes that the DNC breach, the Rich murder, and potential actors in the Trump Russia plot are "things that should be investigated by the intelligence community," to which Gaffney adds, "Specifically by the FBI."
And they were - but the question is to what extent and what will come of it. We know from the document release that the FBI was conducting a SECRET national security investigation into potential State-Sponsored Computer Intrusion with DNC as a victim. Did the investigation into the stolen documents from DNC become an escalated national security matter based on blindly trusted Crowdstrike analysis that it was an attack from a foreign entity?
Was the FBI's false response to Clevenger - saying there were no Rich documents - legal lying since those documents were then related to national security?
Did Perkins Coie, as counsel for victim DNC, have Seth Rich's work laptop? Is Rich's personal laptop still out there? Why are the contents not responsive to the existing FOIA requests?
Markings on the recently released documents show that their classification levels have changed. Were these documents only now released because of their new, lower security levels? Or did the FBI really change their mind about how classified these documents should be?
Is it possible that classification levels changed because the FBI found what Bill Binney and his team of researchers found - that the 'breach' was local and not foreign - meaning it was never a national security matter at all?


