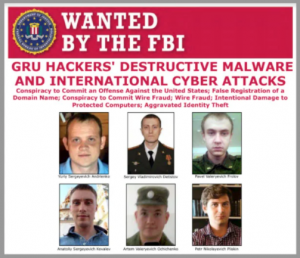
Today’s DOJ announcement, lead by Assistant Attorney General John C. Demers appears to be more than your average Russian conspiracy. The announced charges from a grand jury indictment were leveled against 6 computer hackers who “were residents and nationals of the Russian Federation (Russia) and officers in Unit 74455 of the Russian Main Intelligence Directorate (GRU), a military intelligence agency of the General Staff of the Armed Forces."
The indictment names all six Russian men, who are in their late twenties to early thirties: Yuriy Sergeyevich Andrienko, Sergey Vladimirovich Detistov, Pavel Valeryevich Frolov, Artem Valeryevich Ochichenko, and Petr Nikolayevich Pliskin, as well as Anatoliy Sergeyevich Kovalev, who was previously indicted two years ago for his alleged role into hacking US States' Boards of Election in 2016, according to Wired.com. The indictments, referencing Sandworm, a particularly malicious malware program, is significant because the crimes committed "were against real victims who suffered real harm."
 COURTESY OF DEPARTMENT OF JUSTICE
COURTESY OF DEPARTMENT OF JUSTICE
Wired.com also stated the charges not only represent "the first criminal charges against Sandworm for its most destructive attacks but the first time that most of the charged hackers have been publicly identified as members of the hacker group." The grand jury indictments cover 6 charges related to conspiracy hacking, stealing credentials and passwords, wire fraud, spear phishing, computer fraud of healthcare computer networks, and identity theft.
What makes the activity of these hackers so significant is their use of Sandworm malware and other types of cyberattacks to materially affect people and organizations around the world. While Assistant AG Demers states that "no election interference allegations" were named here, significantly, this team of nefarious 6 co-conspirators launched the first reported attack on control systems of civilian infrastructure:
"In December of 2015 and 2016, the conspirators launched destructive malware attacks against the electric power grid in the Ukraine. These were the first reported destructive malware attacks against the control systems of civilian critical infrastructure. These attacks turned out the lights and turned off the heat in the middle of the Eastern European winter, as the lives of 100’s of thousands (230,000 to be exact) Ukrainian men, women, and children went dark and cold. Their computer attacks used some of the world’s most destructive malware to date, including: KillDisk and Industroyer, which each caused blackouts in Ukraine; NotPetya, which caused nearly $1 billion in losses to the three victims identified in the indictment alone; and Olympic Destroyer, which disrupted thousands of computers used to support the 2018 PyeongChang Winter Olympics."
The NotPetya malware is known as one of the "most destructive and costly cyberattacks ever." It masqueraded as ransomware but this was a "false flag." The conspirators “designed the malware to spread with devastating and indiscriminate alacrity, bringing down entire networks in seconds, and searching for remote computer connections through which to attack additional innocent victims- all without hope of recovery or repair.”
The worm quickly spread globally, shutting down companies and inflicting immense financial harm. Critical sectors of the economy were affected- among which were transportation and healthcare- "not only in Ukraine but as far away as Western Pennsylvania." The indictment includes, "(1) civilian critical infrastructure such as the Heritage Valley Health System, located in....the Western District of Pennsylvania, which had approximately 80 affected medical facilities, (2) a FedEx Corporation subsidiary, TNT Express B.V., which was one of the largest express delivery companies and, (3) a large U.S. pharmaceutical manufacturer, which together had nearly $1 billion in losses resulting from the attacks..."
International attacks were robust and widespread, reaching the 2018 Olympic Games through a spear-phishing campaign called "Olympic Destroyer". The hackers allegedly targeted the games due to their "embarrassment" over "the penalties related to Russia's state-sponsored doping program". They attempted to pin their attack on North Korea, an attempt that eventually failed.
Spear phishing campaigns also targeted several countries including the United Kingdom and Georgia that targeted entities like defense labs and media outlets. In addition, they launched "hack and leak operations in the days leading up to the 2017 French elections".
 John C. Demers, Assistant US Attorney, National Security Division. Credit: AP
John C. Demers, Assistant US Attorney, National Security Division. Credit: AP
Demers was especially acerbic in his remarks about Russia's supposedly good faith offer for a reset in cyber relations between Russia and the United States two weeks ago: "Russia is certainly right that technologically sophisticated nations that aspire to lead have a special responsibility to secure the world order and contribute to widely accepted norms, peace, and security. That's what we're doing here today. But this indictment lays bare Russia's use of its cyber capabilities to destabilize and interfere with the domestic political and economic systems of other countries. Thus, providing a cold reminder of why its proposal is nothing more than dishonest rhetoric and cynical and cheap propaganda."
The department worked on the indictment with authorities in Ukraine, South Korea, New Zealand, Georgia, the U.K., and other governments, as well as Google, Cisco, Facebook, and Twitter. While the likelihood of an appearance by these 6 Russians in an American courtroom is low, the Department of Justice aimed to strongly deter such attacks by foreign agents in the future by bringing forward their dedicated and consequential investigation of the Sandworm Hackers.


